Security
Pernicious Pegasus Plagues (Another) Prime-Minister
With many governments (including the UK Government) being targeted with Pegasus phone-spying software, there’s now news that Spain’s PM’s has also been hit. What Is Pegasus? Pegasus spyware is sold by Israeli-based NSO Group to governments to carry out surveillance by infecting phones with surveillance software. The software is sold to nation states, for millions…
Read MorePegasus Spyware Discovered In Downing Street
The University of Toronto’s Citizen Lab has reported finding evidence that Pegasus spyware was being used to listen-in on UK government networks for 10 Downing Street and the Foreign and Commonwealth Offices (FCO) in 2020 and 2021. Pegasus Pegasus spyware is sold by Israeli-based NSO Group to governments to carry out surveillance by infecting phones…
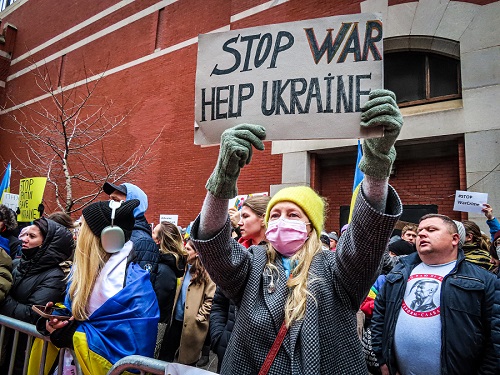
Read MoreWarning: Scam Aid To Ukraine Emails Circulating
The UK’s national fraud reporting centre, Action Fraud, says that it has received 196 reports of scam emails claiming to be raising funds for victims of the war in Ukraine. Facebook Post In a Meta / Facebook post on 18 March, Action Fraud reported: “We’ve received 196 reports about FAKE emails purporting to raise money…
Read MoreGermany Warns Against Use of Kaspersky Anti-Virus
Germany’s Federal Office for Information Security (BSI) has warned that Russia-based Kaspersky’s anti-virus software could be used for spying or launching cyber-attacks. Russian Companies Forced To Launch Cyber-Attacks? The warning was aimed at Russian IT businesses who, claims the BSI, could be used via the software to carry out offensive operations, or forced against their…
Read MoreMobile Malware Surges By 500%
Proofpoint researchers have reported that, starting in early February, there has been a 500 per cent jump in mobile malware delivery attempts in Europe. Trend According to the researchers, this rise is in keeping with a trend that has been evident in the last few years where attackers have been increasing their attempts at smishing…
Read More3% of Users Responsible For 92% Of Breaches
A report by Security Company ‘Elevate’ has revealed that 3 per cent of users are responsible for 92 per cent of malware events for businesses, indicating that a small number of users create the most risk. 2016 to 2021 ‘The Size and Shape of Workforce Risk’ report, conducted on data provided to the Cyentia Institute…
Read MoreOkay, Ukraine Is Being Attacked. How Worried Should We Be?
In this article, we look at how, in addition to the devastating missiles, rockets, bombs, tanks and other weapons, Ukraine has also been the subject of cyber-warfare and we look at how these and other war-related issues could be cause for concern across Europe. War In Ukraine At the time of writing this article, as…
Read MoreWhy Solid Black Bars May Be Best For Redacted Text
In this insight, we look at how to best to avoid redacted text from being ‘unredacted’ by certain software tools, and we look at what researchers advise based on recent experiments. The Problem For businesses and organisations, the increased need for data sharing and/or making some data public can mean that certain (sensitive) parts of…
Read MoreEx School IT Technician Jailed For Cyber Attack
A sacked school IT Technician who took revenge by deleting data and sabotaging his old school’s network (and by wiping the computers of everyone who was logged in) has been jailed. Revenge Hack As reported on Leicestershire Live, a court was told that Adam Georgeson, 29, who was dismissed from his job as an IT…
Read MoreHow Microsoft Will Block Macros To Stop Malware
Microsoft recently announced that it will be blocking Visual Basic for Applications (VBA) macros by default as a way to stop the spread of malware. Since these macros are important automation tools for Microsoft Office apps, how is this going to work? What Are Visual Basic for Applications (VBA) Macros? Visual Basic for Applications (VBA)…
Read More