Security
How To Tell If You’re Being Spoofed
Many cybers attacks now take the form of using fake/spoof communication to trick victims into parting with…
30 Countries Pledge To Act On Ransomware
The international Counter-Ransomware members from 30 countries have issued a joint statement outlining their intent to take…
Proposed Ban For Mass Facial Recognition & ‘Predictive’ Policing
The European Parliament has adopted a resolution calling for a ban on the use of AI-based predictive…
QR Codes … A Security Risk?
In this tech-insight, we take a look at what QR codes are used for, review some well-known…
Domain Security
After a recent report found that poor domain security has left most Global 2000 companies vulnerable to…
Tech Insight: What Is Zero Trust?
With mobile computing, software-as-a-service (SaaS), and now remote working moving the focus of IT security away from…
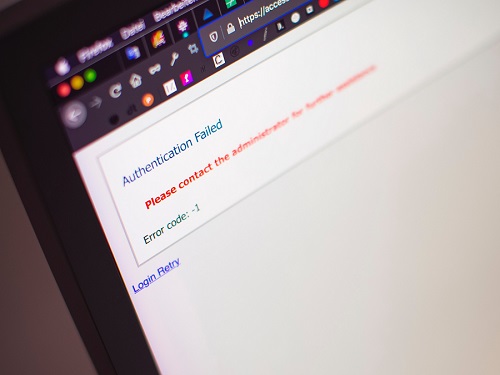
Tech Insight – What Is 2FA?
Two-Factor-Authentication (2FA) refers to another piece of information that users are required to provide (in addition to…
Featured Article – Who Was John McAfee?
After John McAfee was found dead in a Barcelona prison cell last week, we take a brief…
How Secure Is Your Software/Digital Supply Chain?
It is easy to think that cyber-attacks are likely to come from outsiders unconnected to the business,…
Guarding Against The Rise In Router and VoIP Attacks
After a recent high profile media story highlighted how poor router security led to a police raid…